Organizations in Cloud Identity Plane
This article explains the concept of the organization in Cloud Identity Plane and how it is used within the platform.
Concept of the organization
The concept of the organization is utilized when multiple business units within a company would like to consume the Identity and Access Management service(s) deployed as a shared common identity service, such as an internal demo provider, to authenticate their users onto their business tools, applications, or platforms.
Another conceptual application of the organization in CIP supports the B2B2C use case.
Example
If a company wants to be a B2B2C provider, each of the company’s business relationships and users within that business can be represented as an organization.
Role of the organization
Organizations are for grouping users in the CIP system. These disjoint sets of users are useful for restricting the scope of the admin authority. In addition, certain operations may be applied to organizations to affect all member users.
Delegated administration
The User Delegated Administration service allows administrators to manage and administer organizations and users belonging to the organizations in the CIP system.
CIP has a robust set of IAM APIs and a delegated administration model to allow the management of suborganizations and users under them.
This delegated administrative model can be utilized to manage use cases for multiple organizations consuming a single IAM service deployed in the company’s internal cloud and providing a required abstraction at the services and UI level by a flattened data layer model.
General rules that govern the use of organizations in the CIP platform are:
-
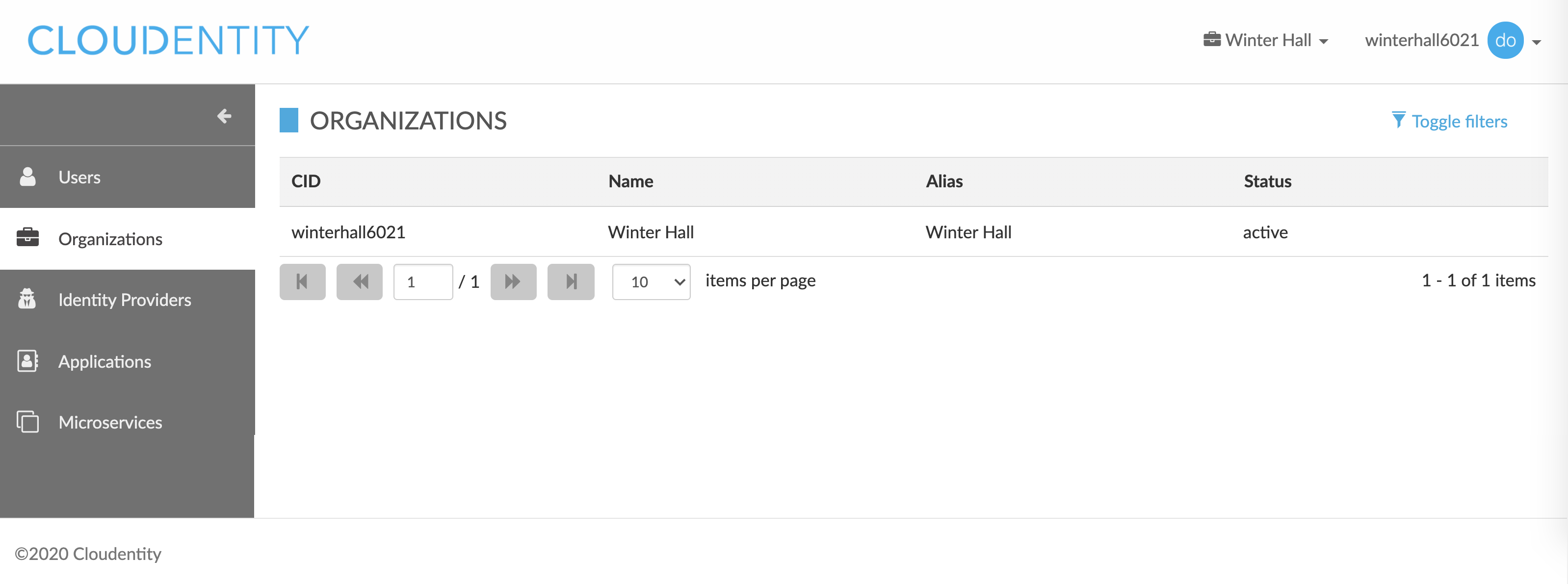
Organizations are uniquely identified by a organization identifier, or CID, which is an addition to the system-generated globally unique key, UUID.
-
Every user in CIP belongs to exactly one organization, which is denoted by an organization CID stored as a user’s organization attribute. This is referred to as a user’s home organization and cannot be changed.
-
When a user authenticates, the user’s home organization is set as a property of the created session. This is referred to as an authenticated user’s session organization.
-
The session organization is the context used for the majority of operations that admins perform on other users, including listing and viewing users. Admins with sufficient privileges are able to change their session organizations.
Organization-specific functionality
In the CIP system, there are a few functions that are organization-dependent and steered from the organization level, such as:
-
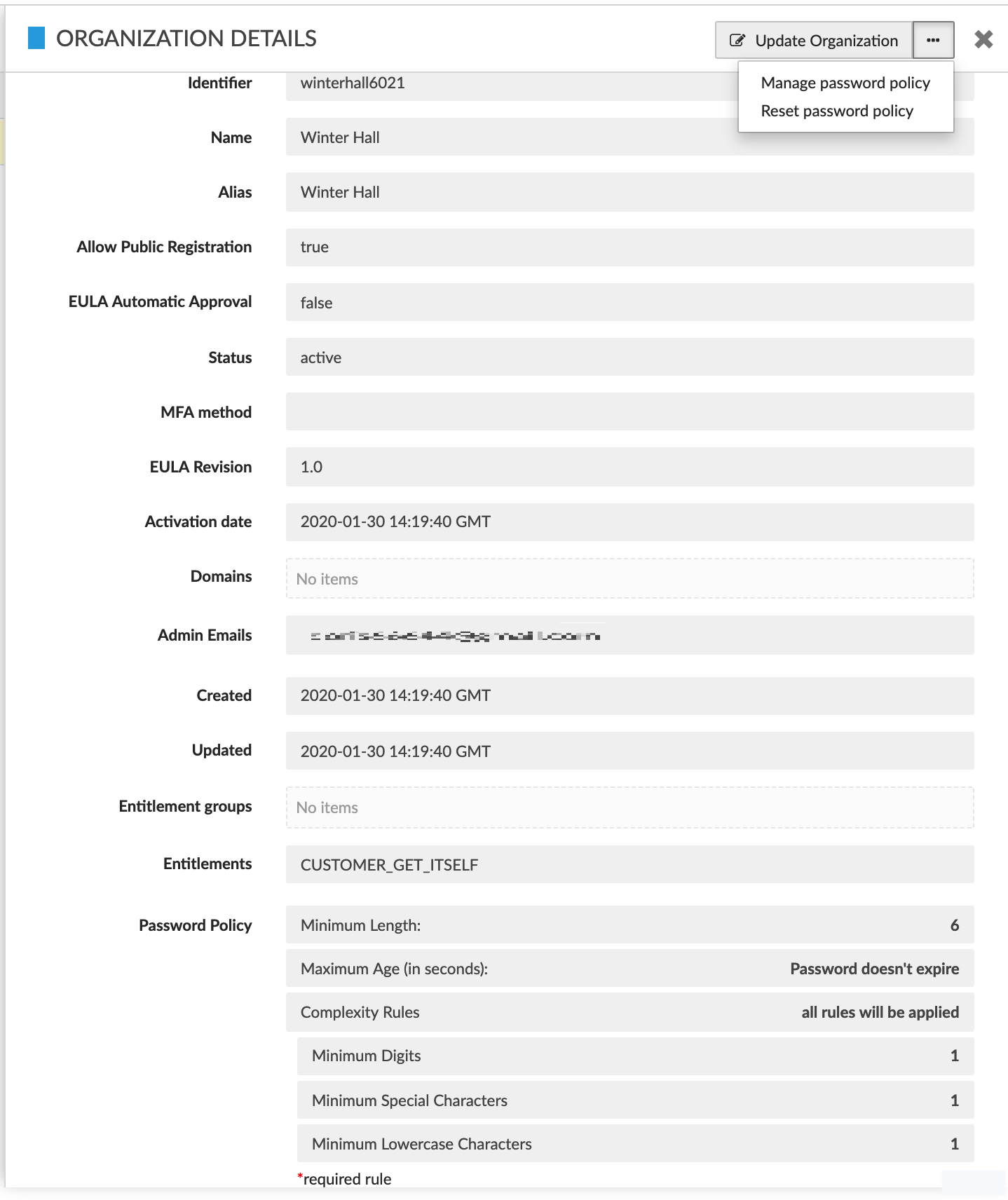
Default MFA method - capability to configure and enforce an organization-specific MFA method
-
EULA-related logic - capability to configure an organization-specific end-user license
-
Password policy - capability to configure an organization-specific password policy
-
External identity provider (SAML/OIDC) - ability to configure an organization-specific SAML/OIDC external identity provider
-
Authentication flow - ability to configure an organization-specific authentication flow
-
Authorization policy - ability to configure an organization-specific logic in the access/authorization policy
-
Permissions and roles - ability to configure organization-specific permissions and roles (requires the CIP Permissions service extension).