About SAML service providers
This article provides an overview of SAML Service Provider integration.
SAML IDP overview
CIP SAML IDP services facilitate the exchange of authentication and authorization information across different organizations with different security domains.
SAML is an XML-based language used to exchange security assertions. SAML defines the following actors:
- Principal - an end user trying to access a resource
- Service Provider (SP) - a web resource that the principal tries to access
- Identity Provider (IDP) - a server that holds the principal’s identities and credentials
In this service, CIP acts as the Identity Provider to generate SAML assertion responses and provide them to any trusted SAML service providers.
SAML profile
One of the most widely used SAML profiles is Web Browser SSO Profile. CIP IDP services support both variants of Web Browser SSO Profile:
- Service Provider (SP) initiated SSO
- Identity Provider (IDP) initiated or Unsolicited SSO
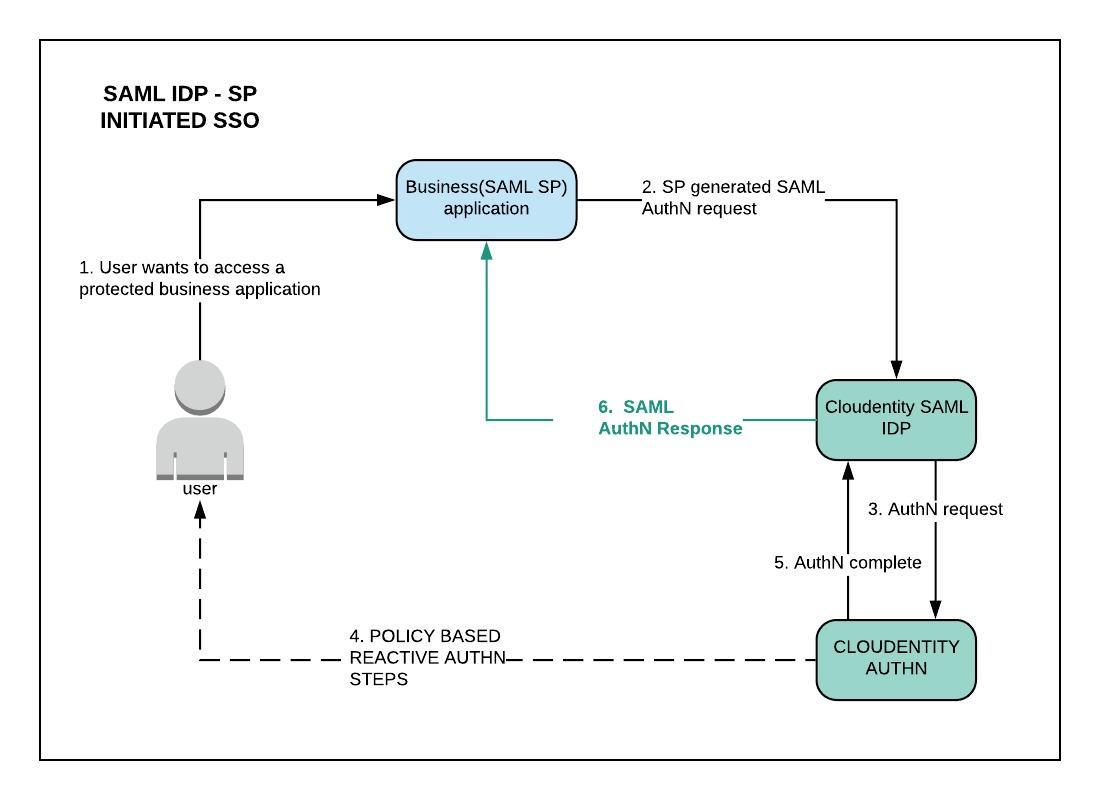
SP-initiated SSO
In the SP-initiated SSO, the user attempts to access a resource on the SP. However the user does not have a current logon session on this site and the user’s federated identity is managed by their IDP. The user is sent to the IDP to log on and the IDP provides a SAML web SSO assertion for the user’s federated identity back to the SP.
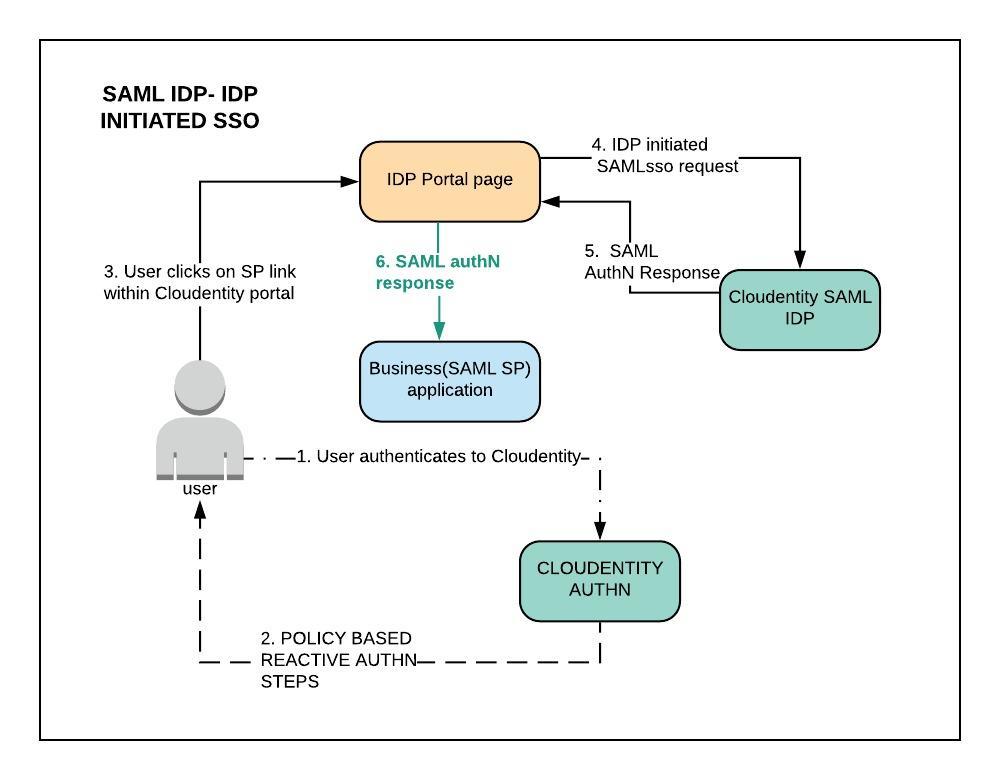
IDP-initiated SSO
In the IDP-initiated SSO, the identity provider is configured with specialized links that refer
to the desired service providers. These links actually refer to the local IDP’s single sign-on
service and pass parameters to the service identifying the remote SP. As a result, instead of
visiting the SP directly, the user accesses the IDP site and clicks on one of the links to
gain access to the remote SP. This triggers the creation of a SAML assertion which
is transported to the service provider using the HTTP POST binding.